


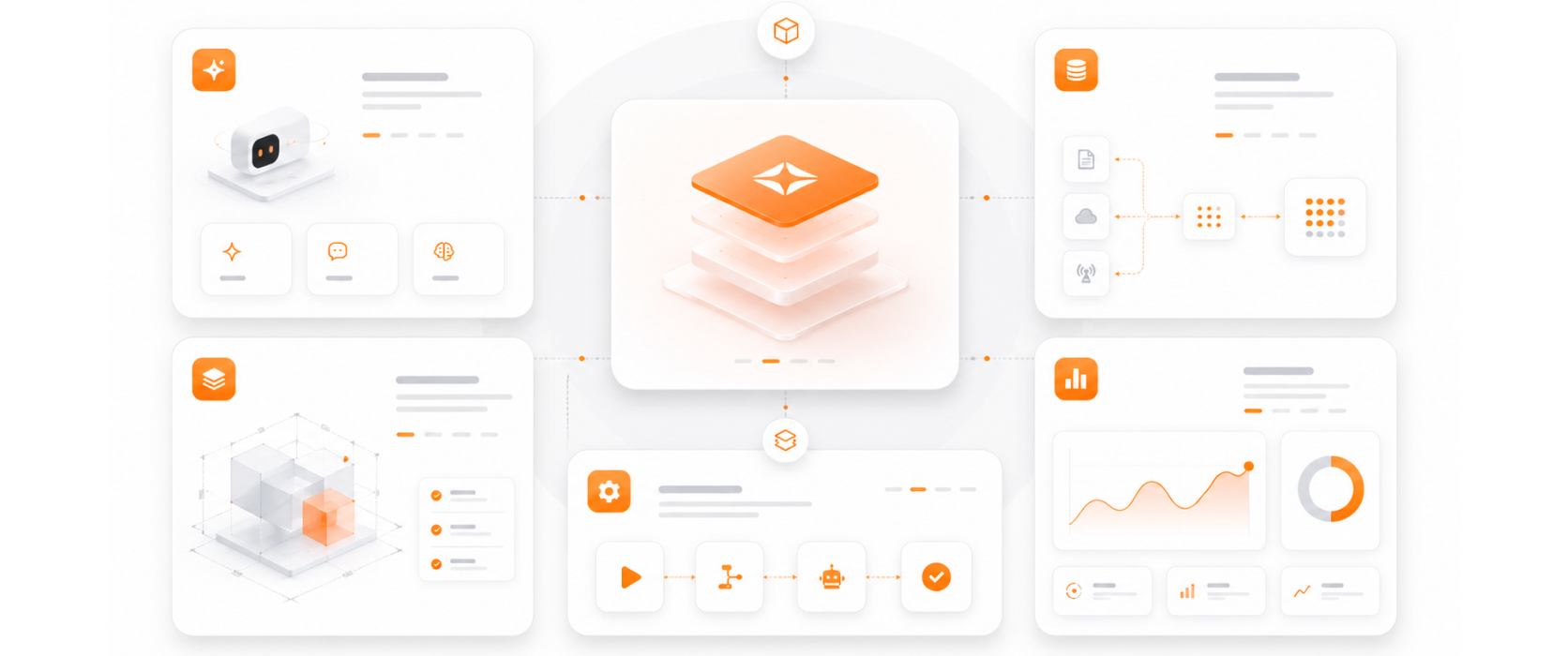
Validated delivery methodology for enterprise endpoint management and security.
Device enrollment, configuration, compliance, and decommission — full endpoint lifecycle management.
Endpoint compliance integrated with identity governance and conditional access — a unified security layer that combines device and identity context.
Endpoint compliance as a Zero Trust enforcement point — devices must meet security standards before accessing any corporate resource.
Intune and Defender for Endpoint can be deployed rapidly across large device estates — delivering measurable security improvement within weeks.