


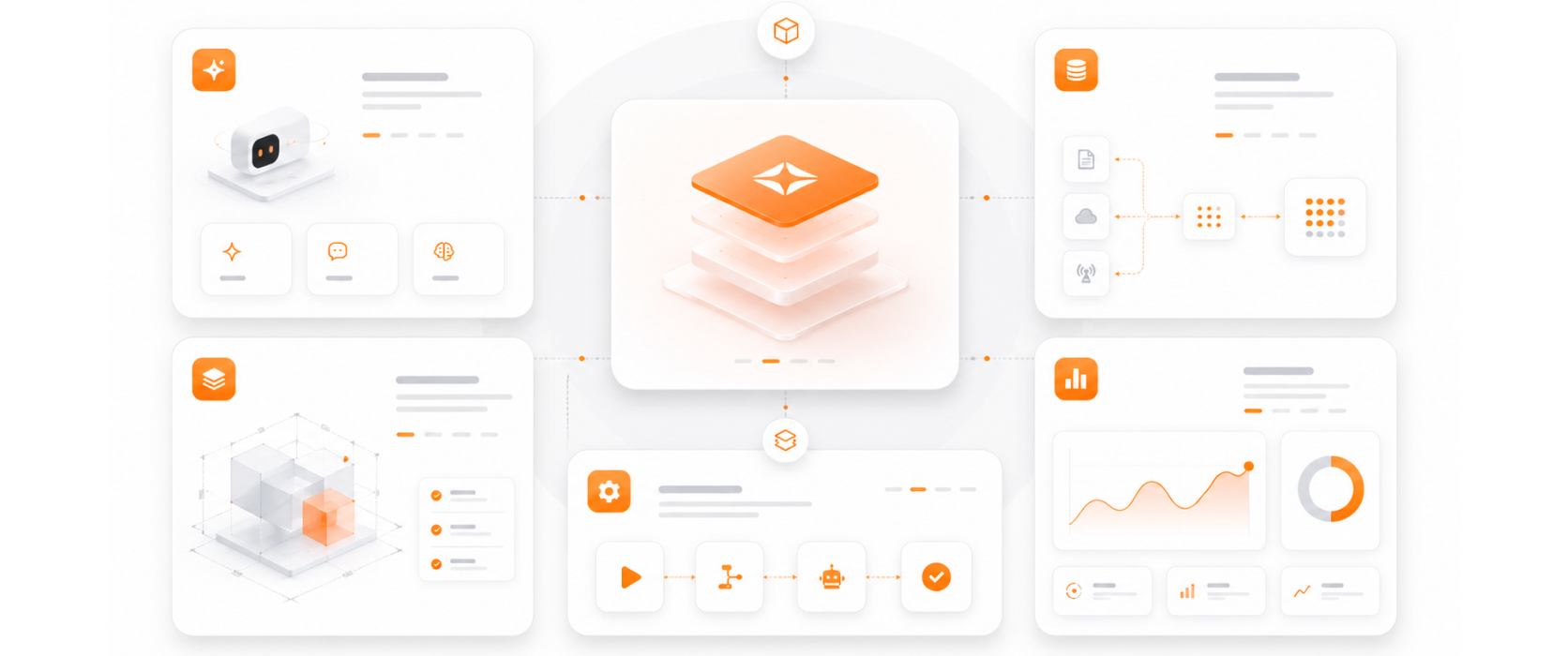
Validated delivery methodology for enterprise IAM at scale.
IAM is the foundation of Zero Trust — we design identity architecture that enforces Zero Trust principles at every access decision.
Azure AD-based identity management across cloud, on-premise, and hybrid environments — a single identity layer for your entire technology estate.
IAM controls designed to meet GDPR, HIPAA, and other regulatory requirements — access governance that satisfies auditors.
MFA enforcement and privileged access management are high-impact, rapid-to-deploy controls — delivering significant risk reduction in the first 30 days.